Introduction
Malaysia stands at the forefront of Southeast Asia’s digital transformation, with its digital economy contributing 22.6% to the national GDP and ambitious plans to reach 25.5% by 2025. This rapid digitalisation has positioned Malaysia as a regional leader in technological advancement, but it has also exposed the nation to an increasingly sophisticated and persistent cybersecurity threat landscape. As businesses, government entities, and individuals embrace digital platforms, the need for robust cybersecurity measures has never been more critical.
This white paper serves as a comprehensive guide to understanding Malaysia’s cybersecurity landscape, examining the current market dynamics, regulatory frameworks, threat patterns, and industry responses. The analysis is designed to educate stakeholders including businesses, policymakers, and IT professionals about the evolving cybersecurity challenges and opportunities in Malaysia. The scope focuses specifically on Malaysia’s unique context within the broader ASEAN region, providing actionable insights for organisations seeking to enhance their cybersecurity posture.
The primary objectives of this white paper are to raise awareness about the current cybersecurity challenges facing Malaysia, propose evidence-based solutions aligned with national strategies, and demonstrate how leading telecommunications and technology providers like CelcomDigi (CD) can serve as trusted partners in addressing these critical security needs.
State of Cybersecurity in Malaysia: A Comprehensive Review
Malaysia’s cybersecurity market is growing robustly. In 2023 it was about USD 1.05 billion, and is projected to reach USD 2.17 billion by 2030 at a CAGR of 11.4%. Factors driving this growth include Malaysia’s ongoing digital transformation (cloud adoption, remote work, new tech like AI/IoT) and rising cyber incidents. Key industry segments (finance, IT, healthcare, education) are increasingly moving online and investing in security. Cyber incidents reached 1,657 in Q1 2025, representing a 7% increase from Q4 2024, with fraud accounting for the majority of reported cases. The country has implemented the landmark Cyber Security Act 2024 and allocated RM421 billion in Budget 2025 for digital infrastructure, including cybersecurity enhancements and funding through agencies (e.g. Finance Ministry’s RM70 million grant to CyberSecurity Malaysia) have boosted market activity. Demand for advanced solutions (cloud security, AI-based threat detection, managed SOC services) continues to rise as organisations seek protection from malware, phishing, and ransomware attacks.
Malaysia’s cybersecurity market is experiencing unprecedented growth, driven by escalating cyber threats and accelerated digital transformation across all sectors. Multiple research sources indicate robust market expansion, though projections vary significantly based on methodology and scope. According to Statista, the cybersecurity market is projected to reach USD 499.63 million in 2025, with a steady annual growth rate of 6.74% through 2030. However, more aggressive projections from Mordor Intelligence suggest the market could grow from USD 0.95 billion in 2023 to USD 2.06 billion by 2028, representing a CAGR of 16.84%.
Several key trends are shaping Malaysia’s cybersecurity market growth. Digital transformation initiatives across government and private sectors are creating new attack surfaces that require advanced security solutions. The accelerated adoption of cloud services and remote work models, particularly post-pandemic, has fundamentally altered the cybersecurity landscape, demanding zero-trust architectures and endpoint protection solutions. Additionally, the proliferation of Internet of Things (IoT) devices and 5G networks is introducing new vulnerabilities that require specialised security frameworks.
Primary drivers of market growth include stringent regulatory mandates such as the Cyber Security Act 2024 and Personal Data Protection Act amendments, which are compelling organisations to invest in compliance-driven security solutions. The increasing frequency and sophistication of cyber incidents with Malaysia recording 74,000 cyberattacks daily in 2023—has heightened awareness among business leaders about the financial and reputational risks of inadequate cybersecurity. Furthermore, the government’s substantial investment of RM1.8 billion through the Malaysia Cyber Security Strategy 2020-2024 demonstrates national commitment to building a resilient cyber ecosystem.
The average spend per employee in the cybersecurity market is forecasted to reach USD 28.39 in 2025, indicating the level of investment organisations are making to protect their digital assets. This investment is particularly crucial given that 53% of Malaysian organisations have either experienced a cybersecurity incident or are unsure due to inadequate forensic capabilities.
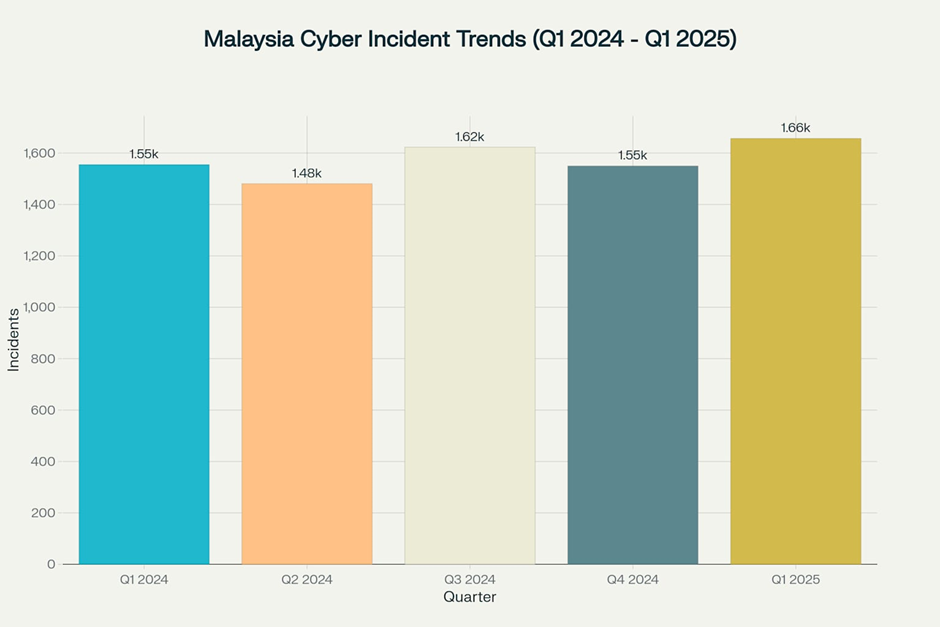
Malaysia Cyber Incident Trends showing quarterly statistics from Q1 2024 to Q1 2025
Current Cyber Incident Landscape
Malaysia’s cyber threat environment remains challenging, with consistent incident levels exceeding 1,500 cases per quarter throughout 2024-2025. The Cyber999 Incident Response Centre recorded 1,550 incidents in Q4 2024, marking a 4% decrease from Q3 2024’s 1,623 incidents, but Q1 2025 saw a rebound to 1,657 incidents.
Fraud dominates the threat landscape, representing 71% of all cyber incidents in 2024, with phishing attacks being the primary attack vector. Data breaches account for 10% of incidents, while intrusion attempts represent 6% of reported cases. The persistence of fraud as the leading threat category reflects the continued effectiveness of social engineering tactics against Malaysian users.
Ransomware Surge
Malaysia experienced a dramatic 153% increase in ransomware attacks in 2024, with 12,643 incidents recorded compared to 4,982 in 2023. This surge places Malaysia among the most affected countries in Southeast Asia, where the region faced an average of 400 daily ransomware attacks throughout 2024.
Ransomware-as-a-Service (RaaS) platforms have democratised these attacks, enabling cybercriminals with limited technical skills to launch sophisticated campaigns.
Phishing and Social Engineering
Phishing attacks decreased in raw numbers but increased in sophistication, with 2,778 cases reported by October 2024 compared to 3,168 in 2023. However, the quality and targeting of attacks have improved significantly.
Regulatory and Policy Environment
Malaysia has developed a comprehensive regulatory framework to address cybersecurity challenges, with legislation evolving to meet the demands of an increasingly digital economy. The Personal Data Protection Act (PDPA) 2010, which came into force in 2013, established the foundation for data protection requirements across commercial transactions. Recent amendments in 2024 have significantly strengthened the PDPA, introducing concepts such as data breach notification requirements, data portability rights, and mandatory Data Protection Officer appointments.
The landmark Cyber Security Act 2024, gazetted on June 26, 2024, and effective from August 26, 2024, represents the most significant advancement in Malaysia’s cybersecurity legislation. This Act establishes the National Cyber Security Committee chaired by the Prime Minister, defines National Critical Information Infrastructure (NCII) entities, and introduces mandatory licensing for cybersecurity service providers. The Act’s extraterritorial application ensures that any entity affecting Malaysia’s NCII, regardless of physical location, falls under its jurisdiction.
The Malaysia Cyber Security Strategy (MCSS) 2020-2024 provides the strategic framework for national cybersecurity implementation, built on five strategic pillars:
- Effective governance and management
- Strengthening legislative framework and enforcement
- Catalysing innovation and R&D
- Enhancing capacity building and awareness
- Strengthening global collaboration.
This strategy allocates RM1.8 billion for cybersecurity initiatives and aims to create over 500,000 high-value digital jobs by 2030.
Key government agencies play crucial roles in implementing these policies. The National Cyber Security Agency (NACSA), established in 2017, serves as the lead agency for cybersecurity matters, with enhanced powers under the new Act to regulate NCII entities and cybersecurity service providers. CyberSecurity Malaysia, operating under the Ministry of Digital, provides specialised cybersecurity services and operates the MyCERT incident response capability, which handles over 1,500 cyber incidents quarterly.
The regulatory impact on businesses has been substantial. The Cyber Security Act 2024 requires NCII entities to conduct annual risk assessments, biennial security audits, and implement sector-specific codes of practice. Non-compliance can result in significant penalties, including fines up to RM500,000 and imprisonment up to 10 years for serious violations. These requirements are driving increased investment in cybersecurity infrastructure and compliance programs across critical sectors including banking, telecommunications, healthcare, and government services.
Threat Landscape in Malaysia
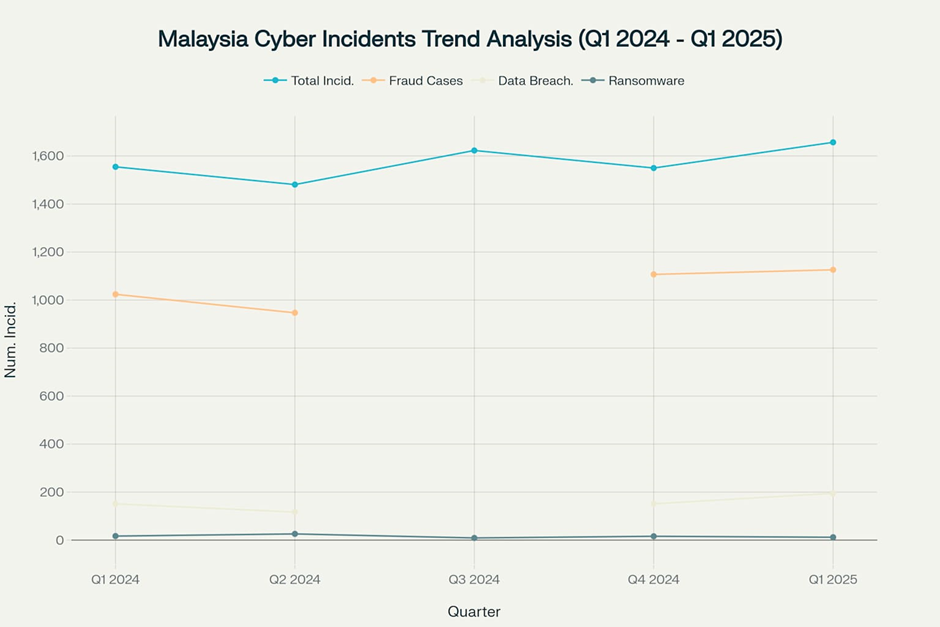
Malaysia Cyber Incidents Trend Analysis showing quarterly data from Q1 2024 to Q1 2025
Malaysia faces a complex and evolving cyber threat landscape that reflects both global trends and region-specific challenges. The country recorded over 1,650 cyber incidents in Q1 2025, representing a 7% increase from the previous quarter, with data breaches increasing by 29% and phishing attacks comprising 68-73% of all fraud cases.
Fraud and phishing dominate the threat landscape, with 1,126 fraud cases reported in Q1 2025 alone. The Cyber999 Incident Response Centre identifies phishing as the most prevalent attack vector, with sophisticated localized campaigns targeting Malaysian users through fake government aid programs, popular e-commerce platforms like Lazada and Shopee, and fraudulent traffic fine notifications. Mobile-based phishing (smishing) is increasingly popular, with attackers impersonating banks, e-wallets, and delivery services to steal sensitive information.
Ransomware incidents showed a 25% decrease in Q1 2025 compared to Q4 2024, with 12 reported incidents. However, the threat remains significant, with businesses being the primary targets and Active Directory servers frequently compromised to enable network-wide encryption. Notable ransomware groups active in Malaysia include LockBit, RansomHub, and Qilin, employing double extortion tactics where attackers both encrypt data and threaten to leak sensitive information.
Data breaches have emerged as a critical concern, with 195 incidents reported in Q1 2025, representing a 29% increase from the previous quarter. High-profile breaches often involve massive datasets containing personally identifiable information (PII) including full names, identification numbers, financial details, and addresses. The trend toward data extortion, where attackers steal sensitive information and demand ransom payments without encrypting systems, is becoming increasingly common.
Emerging threat trends include the rise of AI-powered cyberattacks, with Malaysia experiencing its first reported deepfake financial scam attempt in February 2024. Supply chain attacks are targeting Malaysian organisations through compromised vendors and third-party service providers, as demonstrated by the LYNX ransomware attack on pharmaceutical manufacturer Xepa-Soul Pattinson. IoT vulnerabilities are expanding the attack surface, with Samsung SmartThings and similar platforms being exploited through 20 different security vulnerabilities.
The R00TK1T hacktivist group specifically targeted Malaysia’s digital infrastructure in January 2024, demonstrating how geopolitical tensions can manifest as cyberattacks on national infrastructure. This incident highlighted the vulnerability of government agencies and critical infrastructure to coordinated cyber campaigns.
Recent high-profile incidents include the Kuala Lumpur International Airport (KLIA) ransomware attack resulting in USD 10 million in damages and disrupting critical airport systems. Telekom Malaysia (TM) experienced multiple data breaches affecting Unifi customers’ personal information, including names, identification numbers, and contact details. The Social Security Organisation (SOCSO) – Perkeso suffered a significant cyberattack in December 2023, compromising systems, databases, and websites.
Key Industry Players and Institutions
Malaysia’s cybersecurity ecosystem comprises a diverse mix of local specialists, international corporations, and government agencies working collaboratively to enhance national cyber defenses. The market is moderately consolidated, with several key players dominating different segments of the cybersecurity landscape.
Leading local cybersecurity companies include LGMS (LE Global Services), recognised as one of Malaysia’s most established CREST-accredited cybersecurity providers specialising in penetration testing, vulnerability assessments, and digital forensics. LGMS serves major banks, telecommunications firms, and government bodies, offering PCI DSS audits and ethical hacking capabilities. Wizlynx Group, the Malaysian subsidiary of the Swiss-based company, brings international best practices to the local market with expertise in red teaming, security architecture audits, and cyber risk assessments. Securemetric and Akati Sekurity complete the roster of prominent local players, providing comprehensive cybersecurity solutions tailored to Malaysian market needs.
International cybersecurity vendors have established significant presence in Malaysia, with IBM Corporation leading enterprise-level solutions and maintaining strategic partnerships with local firms like Tech Mahindra to enhance cybersecurity services for Malaysian businesses. Cisco Systems provides advanced networking and security technologies, while other global players including Fortinet, Trend Micro, McAfee, and Palo Alto Networks offer specialized solutions across different market segments.
Government agencies play pivotal roles in Malaysia’s cybersecurity ecosystem. CyberSecurity Malaysia (CSM), operating under the Ministry of Digital, serves as the national cybersecurity specialist centre, providing incident response, malware research, and capacity building programs. The Malaysia Computer Emergency Response Team (MyCERT), established in 1997, operates the Cyber999 hotline and handles over 1,500 cyber incidents quarterly. MyCERT is a member of APCERT and FIRST, facilitating international cooperation in cybersecurity incident response.
The National Cyber Security Agency (NACSA), established in 2017, serves as the lead agency for cybersecurity policy development and implementation, with enhanced regulatory powers under the Cyber Security Act 2024. NACSA operates the National Cyber Coordination and Command Centre (NC4) and is responsible for licensing cybersecurity service providers and regulating National Critical Information Infrastructure (NCII) entities.
Sector-specific collaboration is evident through initiatives like the Malaysia Cyber Security Rating and Common Criteria Evaluation and Certification Scheme (MyCC). Financial sector regulators, particularly Bank Negara Malaysia, have established comprehensive cybersecurity frameworks such as the Risk Management in Technology (RMiT) guidelines, which mandate strict security controls for financial institutions.
These organisations collaborate through various mechanisms including public-private partnerships, threat intelligence sharing, and joint incident response capabilities. The ecosystem’s strength lies in its combination of local expertise understanding Malaysian regulatory requirements and international best practices, creating a robust foundation for addressing evolving cyber threats.
CelcomDigi’s Cybersecurity Solutions Portfolio
CelcomDigi (CD) is a leading Malaysian telecom that offers a broad portfolio of cybersecurity products and services tailored to enterprise needs. With deep experience in mobile, fixed, and cloud infrastructures, CD positions itself as a trusted security partner. Key offerings include:
- Managed Security Services: 24/7 security operations (MSSP) covering threat monitoring, incident detection and response. This includes services like
- Cyber Risk Rating (real-time risk posture assessment)
- Vulnerability Risk Management (continuous scanning and remediation planning)
- Endpoint Security: Solutions such as Endpoint Detection & Response (EDR) for workstations/servers, and Mobile Device Management (MDM) for smartphones/tablets. These protect against malware, phishing, and device-level threats. CelcomDigi also offers a Cyber Guard Device mobile app that uses machine learning to detect attacks on business devices.
- Network Security: Enterprise-grade firewalls, intrusion prevention systems (IPS), secure web gateways, and email security. These control and monitor traffic at the network edge and protect cloud connectivity. For example, CD’s solutions include next-gen firewalls and network access control to segment and isolate threats.
- Cloud and Application Security: Cloud Access Security Brokers (CASB) and web application firewalls (WAF) to secure cloud services and web apps. Workload protection services defend virtual machines and containers. CD partners with vendors like Telefonica Tech to provide Digital Risk Protection (monitoring of brand exposure and phishing sites).
- Data and Identity Security: Data encryption, Data Loss Prevention (DLP), API protection, Privileged Access Management, and source code scanning. These ensure data confidentiality and control access. For instance, CD offers encryption and key-management services, plus DLP to prevent sensitive data leaks.
CelcomDigi’s portfolio (summary):
| Security Domain | Representative CelcomDigi Solutions | Key Benefits |
| Endpoint | EDR, Mobile Device Management, Mobile Threat Detection | Proactive malware/blocking on all devices |
| Network/Perimeter | Firewalls, Intrusion Prevention, Email Security, SWG | Controls network traffic; prevents intrusions |
| Cloud | CASB (Security Access Broker), Web App Firewall, Workload Protection | Secures cloud apps and infrastructure |
| Data & Application | Encryption, DLP, API/DNS Firewall, Source Code Scanner, PAM | Protects sensitive data, APIs, and identities |
| Risk & Compliance | Cyber Risk Rating, VRM, Security Assessments | Improves visibility; prioritises fixes |
CelcomDigi’s solutions map to Malaysia’s threat landscape. For example, its EDR and network IPS address malware and ransomware (which rose 78% in late 2024). CelcomDigi’s managed services provide continuous monitoring, helping enterprises detect sophisticated attacks (e.g. AI-driven phishing) faster.
Apart from these CelcomDigi also provide their
Cybersecurity Hero Products for the SME Market
CelcomDigi’s Hero Product Portfolio for SMEs comprises three integrated solutions, each designed to address specific layers of protection and risk management:
- FortiGate-30G (Network Protection)
- CrowdStrike Falcon EDR (Guarding Endpoints)
- Star Sentry (Stay Informed)
FortiGate-30G (Network Protection)
What Is It?
A next-generation firewall (“digital security guard”) deployed at the network perimeter. It blocks malicious traffic such as hackers and malware from entering an SME’s network, Wi-Fi, or systems.
Key Features
- Enterprise-grade firewall bundled with Unified Threat Protection (UTP) components:
- Intrusion Prevention System (IPS)
- Advanced Malware Protection (AMP)
- Application Control, URL & DNS Filtering, Video Filtering
- Antispam Service
- High performance: Designed to handle real SMB traffic volumes without latency.
- Ease of management: Centralized dashboard for configuration, reporting, and policy updates.
- Cost-effective: SME-friendly pricing with no hidden fees.
- 24/7 technical support: Round-the-clock assistance from accredited professionals.
CrowdStrike Falcon EDR (Guarding Endpoints)
What is it?
- A cloud-native Endpoint Detection and Response (EDR) platform that acts as a “personal bodyguard” for every laptop and desktop. It continuously monitors for suspicious behavior (e.g., lateral movement, fileless attacks) and neutralizes threats in real time.
Key Benefits & Differentiators
- Real-time threat detection & automated response: Reduces dwell time and potential damage.
- Lightweight, cloud-based architecture: Minimal impact on device performance; ideal for SME hardware.
- Easy deployment & scaling: No complex on-prem hardware—just deploy the agent via script or MDM.
- Top-rated by industry analysts: Recognized by G2, PeerSpot, and TrustRadius for efficacy.
- Auto-remediation: Automates investigation and response workflows, cutting manual alert handling by up to 90%.
Star Sentry (Stay Informed)
What is it?
- A continuous cybersecurity assessment and reporting platform likened to a “health check-up” for an SME’s entire security posture. It scans, identifies vulnerabilities, and recommends remediation steps—plus includes protection bundling.
Key Features
- Plug-and-play device with a built-in honeypot that lures attackers to decoy systems, revealing tactics and vectors.
- Unlimited scans (no usage caps) with risk-prioritized reports, clearly indicating the top 10 findings twice per year.
- Proactive health checks that summarize critical vulnerabilities and remediation steps.
- RM 30,000 Cyber Insurance coverage for remedial costs in the event of a breach.
- Bonus: Includes 10 free CrowdStrike Next-Gen Antivirus licenses (worth up to RM 3,000/year).
Case Studies: Effective Cybersecurity in Action
Case Study 1: Financial Institution Strengthens RMiT Compliance Through Comprehensive Security Assessment
A major Malaysian commercial bank faced increasing regulatory pressure to enhance its cybersecurity posture in compliance with Bank Negara Malaysia’s Risk Management in Technology (RMiT) framework. The institution required comprehensive security assessments to identify vulnerabilities, strengthen SOC operations, and improve incident response capabilities while maintaining operational continuity in a highly regulated environment.
The bank partnered with AKATI Sekurity, a leading Malaysian cybersecurity firm, to conduct a comprehensive Red Teaming and Adversarial Attack Simulation Exercise (AASE). This approach simulated real-world attack scenarios to test the institution’s defensive capabilities while identifying gaps in governance, risk management, and compliance (GRC) processes.
The assessment revealed several critical findings: inadequate third-party security oversight, insufficient SOC monitoring capabilities, and gaps in incident response procedures. The bank’s Active Directory security was particularly vulnerable, with potential for lateral movement in case of compromise. Additionally, patch management processes were inconsistent across different system environments, creating exploitable vulnerabilities.
Implementation of remediation measures included:
- Enhanced SOC operations with 24/7 monitoring capabilities and AI-powered threat detection
- Strengthened third-party risk management with mandatory security assessments for all vendors
- Improved incident response procedures with clear escalation pathways and stakeholder communication protocols
- Automated patch management systems with risk-based prioritization
- Regular penetration testing and vulnerability assessments to maintain security posture
Outcomes and lessons learned demonstrated significant improvements in the bank’s security posture. The institution achieved full RMiT compliance within the regulatory timeline, with enhanced threat detection capabilities reducing mean time to detection (MTTD) by 40%. The proactive security measures prevented three potential data breaches during the implementation period, saving an estimated RM2.5 million in potential losses and regulatory penalties.
Key takeaways for other organizations include the importance of regular security assessments, continuous monitoring, and proactive threat hunting. The case demonstrated that compliance-driven security investments can deliver measurable business value beyond regulatory requirements. Most importantly, the integrated approach combining people, processes, and technology proved essential for building sustainable cybersecurity resilience.
Case Study 2: Manufacturing Company Recovers from Ransomware Attack Through Proactive Incident Response
A Malaysian pharmaceutical manufacturing company, Xepa-Soul Pattinson (Malaysia) Sdn Bhd, experienced a sophisticated LYNX ransomware attack that began with targeted phishing campaigns and exploited unpatched vulnerabilities in their IT infrastructure. The attackers successfully encrypted critical systems and exfiltrated 500GB of sensitive data including intellectual property, employee records, and financial information.
The company’s incident response team immediately activated their Business Continuity Plan (BCP), following established protocols for ransomware incidents. Initial response measures included immediate system isolation, forensic preservation, and stakeholder notification to relevant authorities including MyCERT and NACSA. The organization decided against paying the ransom, instead focusing on system recovery and data protection measures.
Recovery strategy involved multiple phases:
- Immediate containment through network segmentation and system isolation
- Forensic investigation to determine attack vectors and scope of compromise
- System restoration from secure backups maintained in air-gapped environments
- Security enhancement including patch management, access control improvements, and employee security training
- Continuous monitoring implementation with advanced threat detection capabilities
Collaboration with cybersecurity partners was crucial for successful recovery. The company engaged local cybersecurity specialists for incident response support, digital forensics, and security architecture review. Government agencies provided threat intelligence and coordination support, while international partners contributed advanced malware analysis and threat hunting capabilities.
Business impact and recovery metrics showed initial disruption lasting 72 hours, with full operational recovery achieved within 10 days. The company’s proactive backup strategy enabled 99.8% data recovery without ransom payment. Financial impact was limited to operational disruption and security enhancement investments, totaling approximately RM850,000 compared to potential losses exceeding RM5 million if systems had been permanently compromised.
Lessons learned and best practices emphasized the critical importance of proactive security measures:
- Regular vulnerability assessments and timely patch management are essential for preventing initial compromise
- Employee security awareness training must address evolving phishing techniques and social engineering tactics
- Backup strategies should include air-gapped systems and regular recovery testing
- Incident response planning must be regularly tested and updated based on emerging threats
- Stakeholder communication during incidents requires clear protocols and transparent reporting
The case demonstrates that well-prepared organizations can successfully recover from sophisticated ransomware attacks while minimizing business impact. The company’s investment in cybersecurity infrastructure and incident response capabilities proved essential for maintaining operational resilience and protecting sensitive data.
Conclusion and Recommendations
Malaysia’s cybersecurity environment is maturing but challenges remain. Market growth is strong, yet threat volumes (especially phishing and ransomware) are rising. Workforce and skills shortages persist, and compliance requirements are tightening. To strengthen cyber resilience, organizations should:
- Adopt advanced security frameworks: Implement Zero Trust architectures and AI-driven defenses. The financial case above shows how zero trust yields concrete benefits. Invest in tools that continuously monitor and correlate events (e.g. next-gen SIEM, MDR).
- Align with regulations and best practices: Ensure readiness for new laws (PDPA amendments, CSA) by appointing DPOs, planning breach notifications, and enforcing policies. Regularly audit compliance with national standards (e.g. RMiT for banks).
- Enhance human and technical defenses: Conduct ongoing staff training (to counter phishing) and run simulated attacks. Deploy multi-factor authentication (MFA) and endpoint security hygiene (patching, backups) to mitigate ransomware (as recommended by Cyble analysts).
- Leverage partnerships: Work with experienced MSSPs and ISPs. CelcomDigi, for instance, offers managed SOC and threat intelligence services tailored to Malaysian businesses. Telecommunication providers like CD can integrate cybersecurity with connectivity (e.g. secure 5G networks, SD-WAN security).
- Invest in emerging tech: Monitor AI-driven threats closely. Fortinet warns that Malaysian organisations see AI-enhanced attacks doubling, including automated social-engineering. Employ AI-based anomaly detection to counter these.
- Collaborate and share intelligence: Report incidents to Cyber999/MyCERT and participate in industry threat-sharing. Government initiatives encourage information sharing (e.g. Cyber Crisis Response Teams) – take advantage of these resources to stay ahead of attackers.
Looking ahead, cybersecurity will remain a top priority. Emerging trends like 5G connectivity, IoT expansion, and AI on both sides of the attack equation mean the landscape will keep evolving. Continuous vigilance, regular investment in defenses, and strong public-private coordination are essential. By following strategic, data-driven cyber practices – and by utilising comprehensive solution portfolios like CelcomDigi’s – Malaysian businesses can turn the cyber challenge into a competitive advantage in the region’s digital economy.